×
The Standard e-Paper
Stay Informed, Even Offline
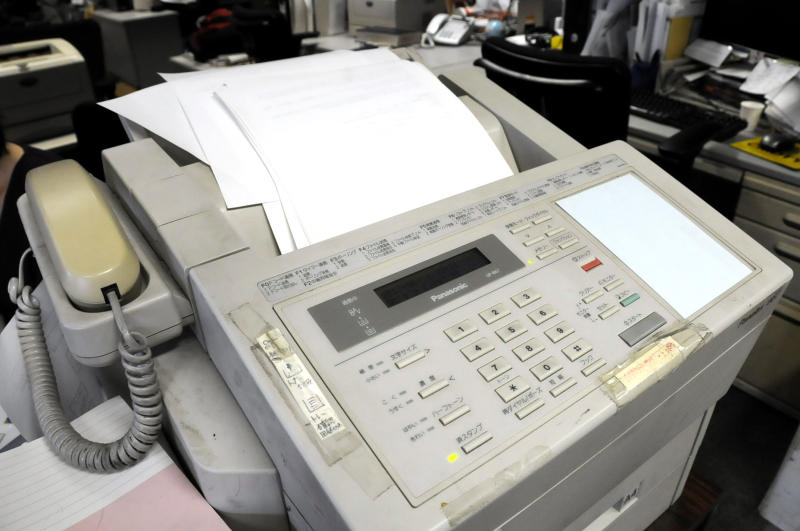
Booby-trapped image data sent by fax can let malicious hackers sneak into corporate networks, security researchers have found.
Since many companies use fax machines that are also printers and photocopiers, they often have a connection to the internal network.